In the realm of cybersecurity, Time-Based One-Time Password (TOTP) tokens have become a popular method for adding an additional layer of security to online accounts. However, the occurrence of TOTP Tokens Out of Sync has emerged as a challenging issue, potentially undermining the very security they aim to enhance. This article explores the nuances of this problem and proposes effective strategies to address it.
Understanding TOTP Tokens Out of Sync
TOTP is a two-factor authentication method that generates temporary codes, usually valid for 30 seconds, to supplement a password during login. The synchronization of these codes between the user’s device and the authentication server is crucial. Out-of-sync TOTP tokens occur when there is a mismatch between the codes generated by the user’s device and the server, resulting in login failures and user frustration.
Causes of TOTP Tokens Out of Sync
Several factors contribute to the occurrence of out-of-sync TOTP tokens:
Clock Drift: Variations in the internal clocks of the user’s device and the authentication server can lead to token mismatches. Even minor clock differences can cause synchronization issues over time.
Network Latency: Delays in communication between the user’s device and the server can cause the TOTP code to expire by the time it reaches the server, leading to discrepancies.
Device Changes: When users switch or reset devices, the initial synchronization might not be seamless, causing subsequent out-of-sync tokens.
One of the common issues associated with Time-Based One-Time Password (TOTP) tokens is clock drift. This problem is particularly relevant when using hardware tokens, where internal clocks are installed and gradually become desynchronized, potentially leading to discrepancies in the generated tokens.
How it Occurs: Hardware tokens are physical devices designed to generate TOTP codes. They typically feature built-in clocks used to calculate the current time and generate temporary codes. However, over time, the internal clocks of these devices can start to slightly lag behind or advance ahead of the actual time.
How to Determine Time Offset and Its Value
To determine the time offset, we recommend using a free utility 2fasolution.com.
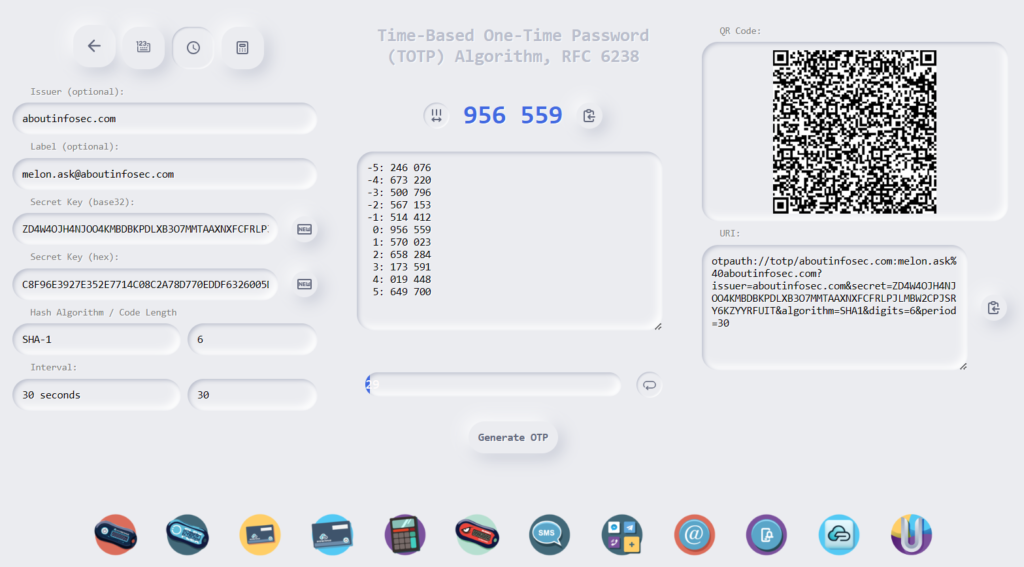
To utilize the utility, you will need to be familiar with the token parameters (Hash Algorithm, Code Length, Time Interval or Period) and its secret key (base32 or hex).
Let’s proceed with generating a one-time password for the TOTP algorithm:
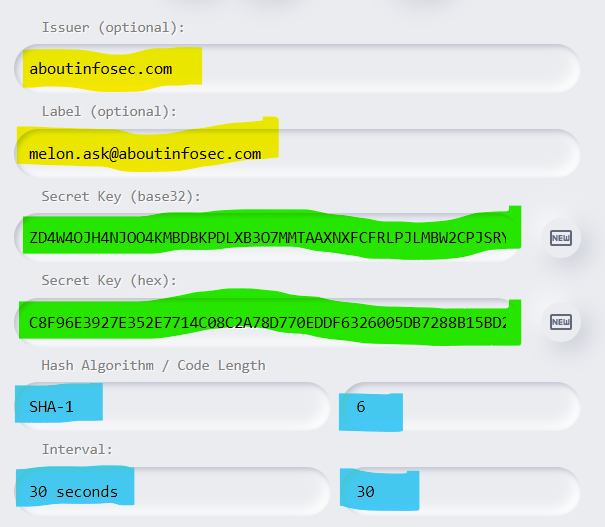
The parameters highlighted in yellow are optional and are used for creating a token using a QR code (URI).
The secret key of the token is embedded within the token itself and should not be extracted from it. If you possess the secret key, you will need to input it into the form in one of the available formats. I’ve highlighted these fields in green.
Ordinary users do not have access to secret keys. “Loss” of the key leads to the discrediting of the token. By “loss,” we mean that the key has fallen into the hands of someone else. In such cases, the token is not recommended for use.
Other important parameters are highlighted in blue. Remember that all parameters influence the correctness of the generated OTP.
Hash Algorithm: Usually, this is SHA-1 or SHA-256. While SHA-1 is considered unreliable, it remains widely used historically.
Code Length: The length of the OTP, usually 6, occasionally 8. You can easily find this by checking your token.
Time Interval or Period: The lifespan of the OTP, typically 30 or 60 seconds. You can also find this information by checking your token.
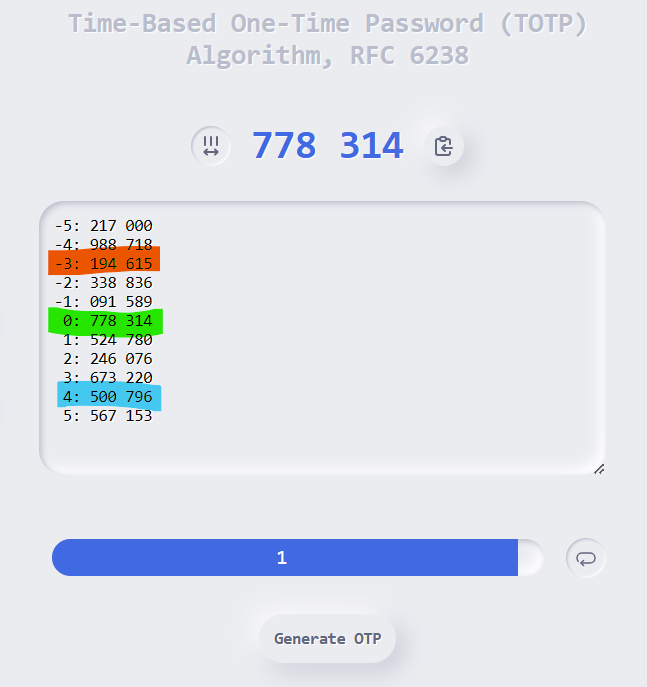
Let’s determine, by example, the time offset of your token.
- If OTP value has an index of “-3” (orange), then your token is behind by 90 seconds (-3 * 30 seconds).
- If your value has an index of “4” (blue), it means your token is ahead by 120 seconds (4 * 30 seconds).
- If the index is “0” (green), then your token’s internal clock is perfectly synchronized.
If you did not find your OTP value in the list, there could be two reasons: you are either using incorrect parameters or a secret key, or your token is out of sync by more than 5 intervals.
Strategies for Issue Resolution
Time Window Extension: Increasing the time window during which a TOTP token is considered valid can accommodate minor clock differences and network delays. However, this approach should strike a balance between security and convenience.
Server-Side Adjustments: Authentication servers can be programmed to accept TOTP codes that fall within a broader range, accounting for potential clock drift.
Push-Based Solutions: Instead of users manually entering TOTP codes, push-based solutions can send real-time authentication requests to users’ devices. This reduces the chances of token discrepancies caused by manual entry errors.
Multiple Time Sources: Implementing multiple time sources for generating TOTP codes, such as syncing with a time server, can mitigate the impact of device clock discrepancies.
- Time synchronization: Software tokens enable time synchronization with an accurate time source, while programmable hardware tokens also allow for precise time configuration.
Advanced Two-Factor Authentication Services: In sophisticated two-factor authentication services, the support for automatic and manual time synchronization between the token and the server is crucial. The integration of these synchronization methods enhances the accuracy of token-based authentication.
Automatic Time Synchronization: In this mode, users are relieved from taking additional steps to synchronize their tokens. During each authentication attempt, the server determines the time offset of the token, adjusting for any time differences. This approach is particularly effective when the token’s clock is ahead. However, when the token’s clock lags, distinguishing whether it’s a clock lag or a delay in user input is challenging for the authentication platform.
Manual Time Synchronization: Regardless, manual intervention remains an option to synchronize the token’s clock with the platform. For this purpose, a two-step input of OTPs, generated in succession, can be introduced into the system. Manual synchronization allows users to explicitly sync their token’s time with the platform. This involves entering two consecutive OTPs generated by the token. The platform uses this information to adjust for any time.
If your token uses other generation algorithms, like HOTP or OCRA, then 2fasolution.com offers more advanced diagnostic tools for these algorithms.





1 comment
Great post. I was checking continuously this blog and I’m impressed! Extremely helpful information particularly the last part 🙂 I care for such information much. I was seeking this certain info for a very long time. Thank you and good luck.