Introduction
In today’s world, the internet has become an integral part of our lives, and we rely on it for almost everything. From communication to online shopping, banking, and socializing, the internet is an essential tool for modern society. However, this dependency on the internet has also led to an increase in cybercrime and online security threats. As a result, it has become necessary to protect online activities from malicious attacks and maintain the privacy and security of online communication.
This is where HTTPS comes into play. HTTPS, or Hypertext Transfer Protocol Secure, is a security protocol that encrypts data sent between a user’s web browser and a website. It is the secure version of HTTP, the protocol that governs the transfer of data between web servers and clients. HTTPS is designed to provide secure communication and ensure that data is transmitted without interception or tampering.
In this article, we will explore what HTTPS is and why it is necessary in today’s digital landscape. We will also look at how HTTPS works and its benefits in ensuring data transmission security, privacy protection, and website authenticity.
How HTTPS Works
HTTPS works by establishing an encrypted connection between a user’s web browser and a website. The encryption ensures that data transmitted between the two parties is secured and cannot be intercepted by attackers.
SSL/TLS Protocols
The foundation of HTTPS encryption is the Secure Sockets Layer (SSL) or Transport Layer Security (TLS) protocol. SSL/TLS protocols use a combination of public and private key encryption to establish a secure connection between a user’s browser and a web server. The SSL/TLS protocol establishes a handshake process between the user’s browser and the web server to negotiate a shared encryption key, which is then used to encrypt and decrypt data transmitted between the two parties.
Data Encryption
Once a secure connection is established using SSL/TLS, data transmitted between the user’s browser and the web server is encrypted using a symmetric encryption algorithm. This means that the same key is used to both encrypt and decrypt data. The symmetric key is negotiated during the handshake process and is unique to each session. The encryption ensures that even if an attacker intercepts the data, they cannot read or modify it.
Certificate Authentication
In addition to data encryption, HTTPS also uses digital certificates to authenticate the identity of the website being accessed. These certificates are issued by trusted third-party Certificate Authorities (CAs) and contain information about the website’s identity, such as the domain name and public key. When a user visits a website using HTTPS, their browser checks the website’s digital certificate to ensure it is valid and issued by a trusted CA. If the certificate is invalid or expired, the browser will display a warning message to the user, indicating that the website’s identity cannot be authenticated.
Overall, HTTPS works by using a combination of encryption and authentication mechanisms to ensure secure and private communication between a user’s browser and a website.
Security Threats and Protection Against Them
As the internet becomes more prevalent in our daily lives, the issue of online security has become increasingly important. The rise of cyber attacks and data breaches has highlighted the need for stronger security measures. In this article, we will explore some of the most common security threats and how HTTPS provides protection against them.
Data Sniffing and Interception
One of the most common security threats on the internet is data sniffing and interception. Hackers can use a variety of tools to intercept and capture data as it is being transmitted across the internet. This can include personal information such as login credentials, credit card numbers, and other sensitive data.
HTTPS provides protection against data sniffing and interception by encrypting all data transmitted between the user’s browser and the web server. This means that even if a hacker intercepts the data, they will not be able to read or use it.
Website Spoofing and Tampering
Website spoofing and tampering are another common security threat. Hackers can create fake websites that look like legitimate ones in order to trick users into entering their personal information. They can also tamper with legitimate websites in order to install malware or steal sensitive data.
HTTPS protects against website spoofing and tampering by verifying the identity of the website using digital certificates. These certificates are issued by trusted third-party authorities and ensure that the website is legitimate and has not been tampered with.
Cross-Site Scripting and Other Threats
Cross-site scripting (XSS) and other threats are also common security concerns. These attacks can be used to steal user data or install malware on the user’s computer.
HTTPS provides protection against XSS and other threats by preventing attackers from injecting malicious code into the user’s browser. This is accomplished through a combination of secure coding practices and encryption.
How HTTPS Protects Against Security Threats
Overall, HTTPS provides strong protection against a variety of online security threats. By encrypting all data transmitted between the user’s browser and the web server, HTTPS ensures that sensitive data remains private and secure. Additionally, HTTPS uses digital certificates to verify the identity of websites and prevent website spoofing and tampering. Finally, HTTPS prevents attacks such as XSS by preventing attackers from injecting malicious code into the user’s browser.
How to Switch to HTTPS
If you have a website, switching to HTTPS is a great way to improve security and protect user data. In this article, we will go over the steps to switch from HTTP to HTTPS.
Step1. Obtaining an SSL Certificate
The first step in switching to HTTPS is to obtain an SSL certificate. This certificate is required to encrypt the data that is transmitted between your website and the user’s browser. There are several different types of SSL certificates available, ranging from basic certificates to more advanced options. It’s important to choose a certificate that fits your needs and budget.
There are several ways to obtain an SSL certificate. Many web hosting providers offer SSL certificates as part of their hosting packages. Alternatively, you can purchase a certificate from a third-party SSL provider.
Step2. Installing an SSL Certificate
Once you have obtained an SSL certificate, the next step is to install it on your web server. The exact process for installing an SSL certificate will vary depending on your web hosting provider and the type of certificate you have purchased. In general, the process involves generating a certificate signing request (CSR), submitting the CSR to the SSL provider, and then installing the certificate on your web server.
Step3. Verifying HTTPS Functionality
After you have installed the SSL certificate, it’s important to verify that HTTPS is working correctly on your website. To do this, simply navigate to your website using HTTPS instead of HTTP. You should see a green padlock icon in your browser’s address bar, indicating that your website is using HTTPS.
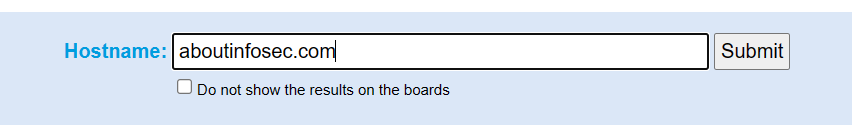
You can also use free online tools such as SSL Server Test to check the functionality of HTTPS on your website and identify any potential issues.
In addition to verifying HTTPS functionality, it’s also a good idea to update any links or redirects on your website to point to the HTTPS version of your site. This will ensure that users are always accessing your site securely. By obtaining an SSL certificate, installing it on your web server, and verifying HTTPS functionality, you can ensure that your website is secure and compliant with modern security standards.

Conclusion
In conclusion, the significance of HTTPS for online security cannot be overstated. With the prevalence of cyber attacks and data breaches, it is more important than ever to take steps to protect sensitive information transmitted over the internet. By using HTTPS, website owners can provide users with a secure and private browsing experience, protecting them from a variety of online security threats.
Best Practices for Using HTTPS to Protect Data
To maximize the security benefits of HTTPS, it is important to follow best practices for using the protocol. These include:
- Obtaining an SSL/TLS certificate from a trusted third-party provider.
- Implementing secure coding practices to prevent attacks such as cross-site scripting.
- Regularly monitoring and updating the SSL/TLS certificate to ensure continued security.
- Using strong and unique passwords for all accounts related to the website.
- Regularly backing up website data to prevent data loss in the event of a breach.
By following these best practices, website owners can ensure that their users’ data is protected and their browsing experience is secure.




1 comment
I consider something really special in this website .