The Social engineering in action is the art of manipulating individuals to gain access to confidential information or to perform unwanted actions. While technological vulnerabilities can be easily fixed, people often remain the weakest link in the security chain. In this article, we will explore several key social engineering tactics and their consequences.
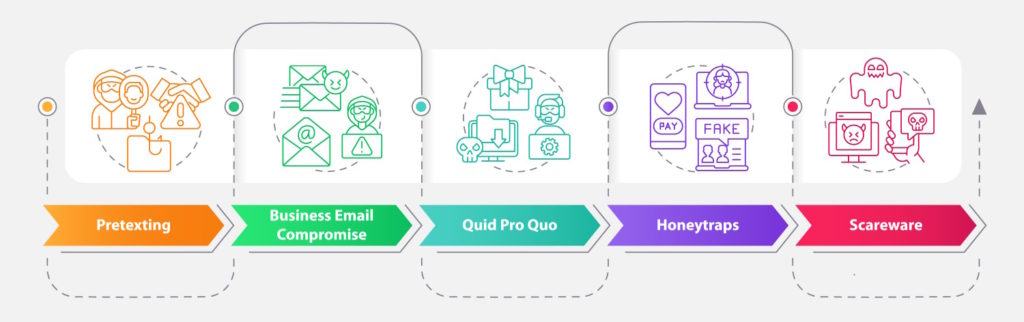

Pretexting
Pretexting is the act of creating a false pretext or scenario that serves as a reason for requesting specific actions or information from a potential victim. This approach allows attackers to create deceptive circumstances to persuade individuals to disclose confidential data or carry out specific actions.
Pretexting is a method in which an attacker impersonates someone else or creates a fictional story to persuade a target into providing information or performing specific actions. For example, an attacker might pose as a technical support representative and request a user’s password for authentication purposes. By employing this technique, an adversary can gain access to systems or confidential information.
Business Email Compromise
Attacks related to Business Email Compromise (BEC) are becoming increasingly prevalent. Attackers masquerade as high-ranking employees or business partners and send emails that demand money transfers or the disclosure of sensitive information. Often, such emails employ subtle psychological pressure to compel the recipient to act quickly and without much suspicion.

Let’s imagine a company called XYZ with a financial manager named Anna. The attacker, having knowledge about the organization and its employee structure, researches information about the company and discovers that Anna is responsible for money transfers. The malicious actor gains access to the email address of a high-ranking executive in the company.
The attacker then poses as the company’s CEO and sends an email to Anna, demanding an urgent transfer of a large sum of money to a specified account. The email uses an official tone and includes details that only the CEO would know.
Under pressure and trusting the received email, Anna proceeds with the transfer, unaware that the email was sent by the attacker. As a result, the funds are transferred to an account controlled by the malicious actor, and the company suffers a significant financial loss.
In this example, the attacker used impersonation and confidence, pretending to be the CEO of the company, to convince Anna to carry out an unwanted action – the money transfer. This type of BEC attack relies on manipulating trust and leveraging an official image, making it particularly dangerous and prevalent in today’s digital landscape.

Quid Pro Quo
The quid pro quo tactic involves offering something valuable in exchange for access to a system or information. For instance, an attacker may offer a free program or service that requires the installation of malware or the provision of personal information. The attacker’s goal is to exploit the obtained data or access for their own interests.
An attacker, pretending to be a technical support representative, calls an office and offers assistance with installing free antivirus software. They claim that remote access to the employee’s computer is required for the software installation. If the employee agrees, the attacker gains full control over the computer and can use it to steal information or perform other malicious actions. In this example, the attacker uses the promise of free software as an enticing “quid pro quo” to gain access to the computer and organization’s information.
Here’s another example of such an attack: An attacker, posing as an employee of a major banking organization, calls a customer and informs them that they are eligible for an exclusive offer of a low-interest rate on a loan. In order to process the loan application, the attacker requests the customer to provide their personal information, including social security numbers and bank account details. When the customer provides these details, the attacker gains access to their financial resources and can carry out fraudulent operations.
In this example, the attacker uses the promise of an attractive financial offer as a “quid pro quo” in exchange for access to the customer’s personal data. The attacker’s goal is to obtain access to the customer’s financial resources and maliciously exploit them for their own interests.
Honeytraps
Honeytraps are strategic methods in which an attacker uses charm, flattery, or even romantic involvement to exploit an individual’s vulnerabilities. The attacker may manipulate the target into revealing sensitive information or granting access to secure systems. Honeytraps can be highly effective due to the emotional and personal nature of the engagement.

An attacker, posing as an attractive individual, initiates an online conversation with the target through a social media platform. They engage in friendly and flirtatious conversations, gradually building a rapport and emotional connection with the target. Over time, the attacker gains the trust of the target and convinces them to share personal or sensitive information, such as login credentials or proprietary data.
In this scenario, the attacker exploits the target’s vulnerabilities by leveraging charm and emotional manipulation. The target, under the impression of a developing relationship, may overlook their usual security precautions and willingly disclose confidential information. The attacker can then exploit this information for their own malicious purposes, such as identity theft or unauthorized access to systems.
This example highlights how honeytraps exploit the personal and emotional nature of human interactions to deceive individuals and gain unauthorized access to sensitive information or systems.

Scareware
Scareware is a tactic that preys on people’s fears and anxieties. Attackers create deceptive pop-up messages or warnings on a victim’s device, tricking them into believing their system is infected with malware or facing a critical issue. The victim is then coerced into taking immediate action, such as purchasing fake antivirus software or revealing personal information.
The victim, while using their computer, suddenly encounters a pop-up window with a warning stating that their system is infected with a dangerous virus and immediate action is required to remove the threat. The pop-up may display alarming messages like “Your computer is at risk” or “Critical system error.” It prompts the victim to click on a button that says “Scan Now” or “Fix the Issue” in order to resolve the problem.
Unaware that it is a scareware tactic, the victim clicks on the button, believing they are taking necessary steps to protect their system. However, instead of conducting a genuine scan or fixing any issue, the pop-up redirects the victim to a fraudulent website that offers fake antivirus software. The victim, driven by fear and urgency, may proceed to purchase the software or provide personal and financial information to complete the transaction.
In reality, the scareware program is not a legitimate antivirus solution, but rather a deceptive tool used by cybercriminals to deceive users and extract their money or personal information.
This example illustrates how scareware manipulates people’s fears by presenting false threats and urgent warnings, leading them to take actions that benefit the attackers.
Conclusion
Understanding the various social engineering tactics is crucial in combating cyber threats. By being aware of these manipulation techniques, individuals and organizations can implement robust security measures and educate their employees to recognize and resist such attacks. Building a strong human firewall is essential to safeguarding sensitive information and mitigating the risks associated with social engineering tactics.