Introduction
Nowadays, many people are familiar with hardware 2FA tokens for two-factor authentication. These small devices are capable of generating one-time passwords. They all seem to have similar components: a casing, a display, and a button. But are they all the same? Why do manufacturers often offer multiple models in their product line? Let’s delve into this together.
Our partner Protectimus has provided us with three token models for review: TWO, SHARK, and FLEX. We were curious about the meaning behind these names and whether they hold any significance or are merely arbitrary.

It turns out that TWO represents the second generation of tokens, boasting a more robust casing and a longer battery life.
On the other hand, SHARK symbolizes power and reliability. This token supports the advanced SHA-256 algorithm, providing enhanced protection against brute force attacks.


FLEX signifies flexibility and adaptability, as this model is programmable, allowing users to set a secret key, the lifespan of the one-time password, and even synchronize the exact time.
It makes one wonder what they would name a token with the SHA-512 algorithm—perhaps MEGA SHARK?
Key parameters
Let’s consider the key parameters of the tokens:
|
|
TWO
|
SHARK
|
FLEX
|
|---|---|---|---|
|
OATH Algorithm
|
|||
|
Programmable
|
-
|
-
|
+
|
|
Hash Algorithm
|
SHA-1
|
SHA-256
|
SHA-1
|
|
OTP Length
|
6
|
6
|
6
|
|
OTP Lifetime
|
30
|
30
|
30 , 60
|
|
Tyme Sync
|
-
|
-
|
+
|
|
|
|||
|
|
By offering a range of choices, manufacturers aim to provide users with flexibility and reliability when selecting a hardware token for their two-factor authentication needs. Users can choose tokens based on their preferences and security requirements, ensuring the utmost protection for their accounts and data.
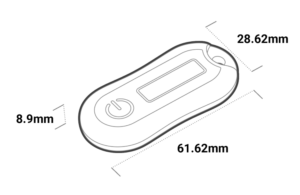
All of these tokens have the same casing; the only difference lies in the design of the front and back panels and the internals.
TWO vs SHARK
Let’s compare the TWO and SHARK tokens. These tokens come with a pre-set secret key and can be used in systems where custom secret keys can be set. Let’s focus on the differences, specifically the hashing algorithms: SHA-1 for TWO and SHA-2 for SHARK. The latter is more secure and recommended for the development of new systems. SHA-1 is more widely used due to historical reasons.
Remember that the authentication platform must support the corresponding hashing algorithm. Simply purchasing a token with SHA-2 support is not sufficient. However, if you use the Protectimus service and platform, you can utilize various hashing algorithms, including SHA-512.
TWO vs FLEX
Let’s now compare TWO and FLEX tokens. These tokens have the same SHA-1 hashing algorithm. The main difference lies in the fact that FLEX can be reprogrammed an unlimited number of times using a free application from Google Play and an Android phone. This capability allows you to add the token to systems where you don’t manage the secret keys by flashing the secret key into the token.
Thus, you can easily replace applications like Google Authenticator, Microsoft Authenticator, or Protectimus Smart with the reprogrammable FLEX token.
Please note that FLEX supports storing only one secret key at a time, unlike software tokens on smartphones.
Reprogrammable FLEX tokens offer an unprecedented level of security because no one, not even the manufacturer, will know the secret key of your token.
During the reprogramming (burning) process, you can set the lifetime of the one-time password to either 30 or 60 seconds. With each secret key burn, the exact time of the secret key is set.
Typically, in physical tokens, the time is not adjustable, and in case of time discrepancy, the authentication platform takes care of synchronization. The Protectimus platform and service support automatic synchronization (adjustment to the time shift) of hardware tokens.






What are hardware 2FA tokens (TOTP) best suited for?
- Hardware tokens are best suited for corporate users who want to avoid the hassle of configuring tokens for each individual in the company. It provides a more reliable and cost-effective solution compared to regular SMS authentication, especially for regular usage.
- TOTP tokens are also suitable for systems with interfaces that are difficult for attackers to counterfeit.
Web interfaces are often vulnerable to spoofing, where an attacker can redirect you to a fake resource, for example, through phishing, and obtain all your authentication credentials.
For web pages and transaction authentication, it is necessary to use algorithms and technologies that allow binding the user’s context (environment, transaction, key operation data) to the input data on which the OTP is generated.
Сonclusion
And don’t forget, when it comes to buying the perfect hardware token for your two-factor authentication needs, it’s best to consult with the experts. They’re like the gurus of security, offering their precious wisdom and advice. And the best part? Their consultations are usually free! Well, almost free. You might have to pay for the actual token itself, but hey, expert knowledge is priceless, right? So go ahead, seek their guidance, and make a wise and secure purchase decision.
However, keep in mind that if you purchase tokens and they don’t meet your requirements, it’s unlikely that you’ll be able to return them. So choose wisely and make sure the tokens are the perfect fit for your needs!




1 comment
There is noticeably a bundle to know about this. I assume you made certain nice points in features also.